Social networking websites have helped people around the world share messages, pictures, files and even real-time information about what they are doing and where they are. According to Statista, the average person spends approximately 151 minutes on social media every day, an incredible amount of time spent on a relatively recent phenomenon.
Although these networks can be instrumental in fostering social interactions both online and offline, social media is also making information accessible to people who want to abuse it. The most popular social media platforms have billions of users, and the number keeps growing every year.
Consequentially, the scope and depth of information shared has grown exponentially. As a best practice, it's essential that users be aware of their privacy and security settings, and issues that may arise due to sharing. Before you utilize any social networking platform, it is essential to understand how your data may be left vulnerable, and how to protect yourself and the people you work with.
The following article provides security tips to help you safeguard your personal and corporate social media accounts.
Securing Corporate Social Media Accounts:
Social media can be used by businesses to advertise and establish their brands. Since most corporate profiles are open to the public, they are vulnerable to hackers. Furthermore, the rate of attacks on corporate social media accounts has increased, especially with Twitter.
Below are some best practices for corporate accounts:
.png?width=320&height=800&name=Securing%20Accounts%20(1).png) 1. Practice Good Password Hygiene:
1. Practice Good Password Hygiene:
Ensure that you change your social media passwords regularly and that passwords are meaningless strings of letters, numbers and special characters. Make sure that you don’t write down your passwords, and don’t share them with others.
2. Check Access Rights for External Tools:
There are hundreds of tools available that can help you manage your social media accounts, such as HubSpot, HootSuite and Buffer. It’s important to audit which apps have access to your accounts regularly. Revoke access if you no longer use a particular tool.
3. Educate Employees:
It's crucial that your organization knows what to look out for regarding suspicious behavior on company accounts and personal accounts. If a member of your team has their account hacked, the hacker may well target their place of work first, and post unsavory messages on your company’s social channels. Since the employee's personal and work accounts could be interconnected, the hacker might use the compromised personal account as a gateway to gain access to the company's internal systems or information.
4. Limit Access:
The fewer people with access to company social media accounts, the better. This makes it easier to monitor posts and avoid any deliberate sabotage.
5. Develop a Social Media Security Policy:
A formal social media policy means that everyone can be aware of standards and expectations. Corporations can significantly reduce risk by developing a social media security policy that governs the use of social media by employees and the company as a whole.
6. Put Someone in Charge:
Rather than giving access to everyone on the team and then spending valuable time trying to monitor channels, consider having a key person act as the eyes and ears of your social presence. A designated manager and gatekeeper can go a long way toward mitigating risk.
Securing Personal Social Media Accounts:
Each social media platform has its own security features that you should read carefully and leverage.
Below are some best practices for personal accounts:
1. Set Up Your Security Answers:
Two-factor authentication is available for most social media sites. Many experts recommend that you answer these questions with randomized or illogical answers, as some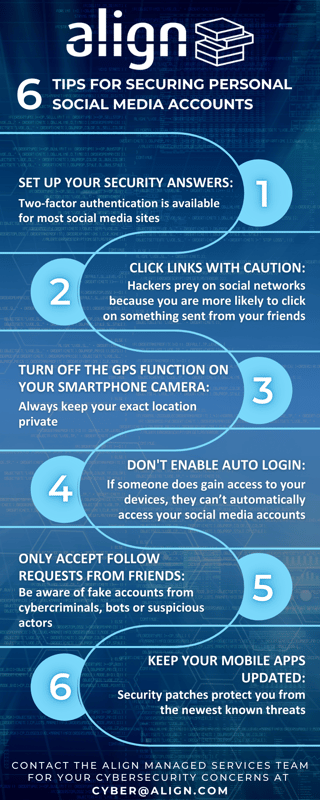 questions (like your mother’s maiden name), can be looked up or guessed, creating a vulnerability instead of strengthening protection.
questions (like your mother’s maiden name), can be looked up or guessed, creating a vulnerability instead of strengthening protection.
2. Think Before You Click Links:
Be wary even if they appear to be from someone you know. Hackers prey on social networks because you are more likely to click on something sent from your friends. When in doubt, hover over the link to see the URL, and avoid anything suspicious.
3. Turn Off the GPS Function on Your Smartphone Camera:
If you plan to share images online, make sure that you turn off the GPS on your device to keep your exact location private.
4. Don’t Enable Auto Login:
Make sure that you don’t have your apps set to log you in automatically, and that you don’t have your computer’s browser “remember” your login and password. That way, if someone does gain access to your devices, they can’t automatically access your social media accounts.
5. Be Frugal with Random Friend Requests:
Unless the purpose of your social media account is to promote a business, don't accept friend or follow requests from people you don't know, even if it looks like you have friends in common. They may be fake accounts from cybercriminals, bots or suspicious actors.
6. Keep Your Mobile Apps Updated:
Make sure you have the latest version of the platform you’re using. Security patches protect you from the newest known threats. Waiting too long to install updates could expose you to severe vulnerabilities.
Even after following best practices, there is always a chance that a hacker could compromise your data. To ensure your information is secure and business assets are safeguarded, we recommend employing a reputable cybersecurity advisory practice. When it comes to your firm's cybersecurity, don't wait until it's too late.
Align Cybersecurity offers tailored, layered and advanced cybersecurity solutions encompassing Vulnerability Assessments/Penetration Testing, Cybersecurity Risk Management as a Service (Align Risk CSR), Customized Cybersecurity Programs, Third Party Management, Managed Threat Protection (Align Guardian), Cybersecurity Training and more.



