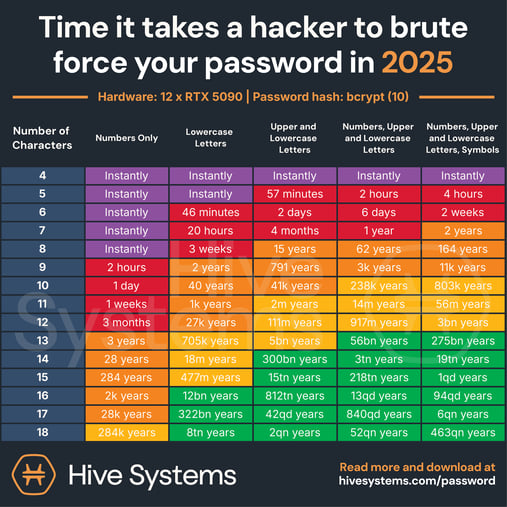
Hive Systems has updated its famous Password Table for 2025. Their latest data shows the updated time it takes for hackers to "brute force" a password, taking today’s newest technologies into account. Read on to learn what the latest data reveals and how to protect your organization with stronger password policies.
Robust Password Security is Critical to Today's Workplace
The advances in technology (specifically in affordable cloud computing) over the past few years have dramatically shortened the amount of time it takes to crack a password.
The ability to crack longer, more intricate passwords is even more threatening when you consider today’s distributed or hybrid workforces. As professionals regularly began logging in from miles apart and relying on personal and public Wi-Fi networks—as well as their own insecure devices—organizations’ internal networks became wide open to risk, fundamentally altering the traditional office security perimeter.
Securing systems and devices against growing cyberattacks has never been more important, beyond just network and email security. And while organizations have attempted to combat cybersecurity risks and other issues head-on, scaling back and prioritizing basic 101-level password hygiene and policies before implementing more sophisticated software might be where most organizations need to focus on. Aka—the password.
How to Build, Store and Maintain Strong Passwords
So, how can companies keep their professionals secure if half their workforce is remote but still need to access mission-critical applications outside of the enterprise network?
It can be as simple as creating and implementing strong password policies. In fact, most businesses don’t fully understand the spectrum of threats directly caused by poor password hygiene. The good news is that building a strategy for password use within a larger company cybersecurity program is more simple than it used to be, thanks to password security and management becoming more intuitive in the last few years.
When developing a robust password strategy, you can follow password best practices from the National Institute of Standards and Technology (NIST) or other leading security organizations. Here are some potential risk-reducing best practices:
- Set a minimum password length. NIST recommends eight characters, but based on Hive’s table, you should use 12 characters with both upper- and lower-case letters, numbers, and symbols.
- Use a password manager. These store logins in a vault and protect them via a master password or biometric login options. They can generate unique passwords based on preferred length and complexity, and help users avoid password reuse.
- Employ a user verification policy. This can be done through two-factor or multi-factor authentication. It ensures an agent won’t give an unauthorized user access without knowing it, protecting an organization while also ensuring continuity between a distributed workforce.
- Implement employee awareness training. Address the fundamentals of proper password hygiene year after year, ensuring your policies and expectations evolve alongside new cyber risks and technology.
Why Does This Matter?
We live in a time of heightened cyber risks, and not just because workforces continue to connect remotely.
Focusing on improving passwords might seem fundamental, but it allows companies to ultimately maximize workforce continuity and stability in order to meet today’s challenges directly, safely, and flexibly.
Align Cybersecurity™
Align Cybersecurity, Align's comprehensive risk management solution, offers engaging, advanced security awareness training, in addition to, custom “white-glove” in-person training, mock cybersecurity exams and reporting of education, retention and employee performance relating to cybersecurity risk.
For more information regarding our award-winning Cybersecurity Advisory Services, visit here or contact us by clicking the button below.




